Understanding Age Verification
The digital landscape has fundamentally transformed how businesses verify the ages of their users. Throughout my career helping companies navigate regulatory compliance, I've witnessed the dramatic evolution of age verification requirements—from simple checkbox confirmations to sophisticated biometric systems.
Today, age verification systems are no longer optional for many businesses; they're a regulatory imperative backed by serious legal consequences.

The Legal and Regulatory Landscape
The regulatory environment has become increasingly complex and unforgiving. The Online Safety Act 2023 in the UK now mandates strict age verification for platforms that could expose children to harmful content. I've personally guided several clients through compliance with this regulation, and the requirements are substantial. In the United States, the Children's Online Privacy Protection Act (COPPA) has long required businesses to obtain verifiable parental consent before collecting data from children under 13. Meanwhile, the General Data Protection Regulation (GDPR) adds another layer, demanding that businesses handle personal data with extreme care during the verification process.
Know your customer (KYC) regulations further complicate the picture, particularly for financial services and online gambling platforms. When I work with these clients, regulatory compliance isn't just about avoiding fines—it's about operational survival. The penalties for non-compliance can reach millions of dollars, not to mention the devastating reputational damage.
The Business Case for Robust Age Verification
Beyond regulatory compliance, I've seen robust age verification systems deliver tangible business benefits for my clients. One e-commerce client reduced fraud by 47% within six months of implementing proper verification. Age verification systems strengthen computer security infrastructure by adding authentication layers that deter malicious actors.
More importantly, customers increasingly expect businesses to protect minors online. Companies that implement verification properly gain competitive advantages through enhanced trust and brand protection. The investment in age verification software pays dividends far beyond simply avoiding regulatory penalties.
What is Age Verification Software?
Age verification software represents specialized technology that confirms a user's age before granting access to age-restricted content, products, or services. Throughout my implementations across diverse industries, I've seen these identity verification services evolve from simple self-declaration systems to sophisticated platforms leveraging artificial intelligence, biometrics, and document authentication.
Modern age verification systems integrate seamlessly with existing software infrastructure through APIs and SDKs, making deployment faster than many business owners anticipate. The authentication processes vary depending on the risk level and industry requirements, but all share a common goal: confirming user age with sufficient certainty to satisfy legal requirements while maintaining reasonable user experience.
How Age Verification Software Works
Age verification systems employ multiple methodologies, each with distinct advantages and appropriate use cases. In my experience implementing these systems, understanding the technical foundations helps businesses make informed decisions about which approach best serves their specific needs.
The most sophisticated age verification systems utilize facial recognition technology and biometric analysis to estimate age from user photographs. I've deployed these systems for clients in highly regulated industries, and when implemented correctly, they achieve remarkable accuracy while processing verifications in seconds. The technology analyzes facial features, skin texture, and other biological markers to estimate age, typically with accuracy within 2-3 years.
Identity document verification remains the gold standard for high-assurance applications. When I implement document verification systems, they typically capture images of government-issued IDs, extract data using optical character recognition, verify document authenticity through security feature analysis, and often include facial comparison between the ID photo and a user selfie. This multi-factor approach substantially reduces fraud while maintaining regulatory compliance.
Key Methods and Technologies
Through years of implementing various verification approaches, I've developed clear perspectives on when each method works best:
| Method | Accuracy | User Friction | Speed | Privacy Impact | Best Use Cases |
|---|---|---|---|---|---|
| Identity Document Verification | 95-99% | Medium | 30-90 seconds | Medium | Online gambling, financial services, alcohol sales |
| Facial Recognition System with Age Estimation | 85-95% | Low | 5-15 seconds | Low-Medium | Social media, gaming platforms, content streaming |
| Biometric Analysis | 90-97% | Low | 10-30 seconds | Medium | Enterprise applications, high-security environments |
| Database Cross-Reference | 80-90% | Low | Instant | Low | E-commerce, subscription services |
| Credit Card Verification | 70-85% | Low | Instant | Low | Digital content purchases, app stores |
Machine-readable passports and enhanced driver's licenses with embedded chips provide the highest verification confidence. In my implementations for enterprise clients, these documents offer machine-readable data that dramatically accelerates verification while reducing manual review requirements. Optical character recognition technology extracts text from identity documents with 98%+ accuracy when properly configured, though I always recommend human review for edge cases.
I've found that document verification excels when businesses need legal defensibility and high assurance, though it creates more user friction. Conversely, biometric age estimation works beautifully for scenarios prioritizing user experience over absolute certainty—social media platforms being a prime example from my client work.
Age Verification Systems Explained
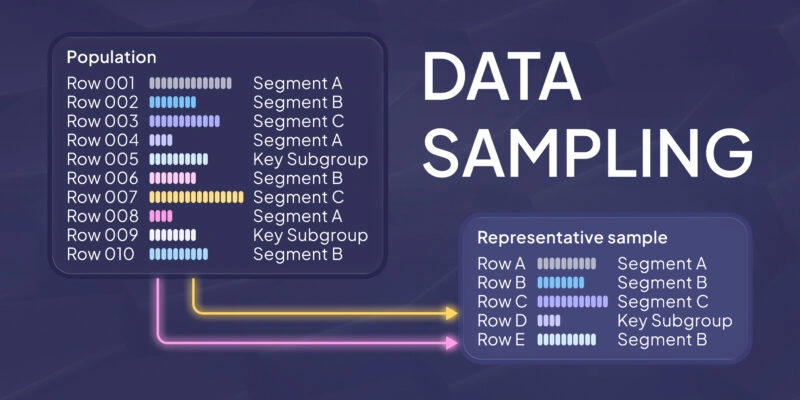
Age verification systems integrate multiple technologies into cohesive workflows. In a typical implementation I oversee, the system receives user data through an API call from the client's application, processes this information through verification engines, encrypts sensitive data using industry-standard encryption protocols (typically AES-256), performs authentication checks against multiple data sources, and returns a verification result with confidence scoring.
Modern age verification systems leverage robust API architectures that enable real-time verification. When I work with development teams, I emphasize the importance of API security, rate limiting, and proper error handling. The authentication layer ensures that only authorized applications can access verification services, preventing unauthorized use and potential abuse.
The Verification Process: From User Input to Confirmation
Let me walk you through a typical verification flow that I've implemented dozens of times:
- User initiates verification – The customer attempts to access age-restricted content or complete a purchase
- System collects data – Depending on the method, this might be a photo, ID document, or database information
- Data transmission – Information is securely transmitted (encrypted) to the verification service
- Authentication occurs – The system validates identity documents, performs liveness detection for photos, cross-references database records
- Verification decision – The system determines pass/fail based on confidence thresholds
- Result delivery – The client application receives the verification status
- Personal data handling – Sensitive information is minimized, encrypted, or deleted per retention policies
User experience considerations are paramount. I've seen clients lose significant conversion when verification processes exceed 60 seconds or require more than three user actions. The key is balancing security requirements with practical usability—something I refine continuously based on analytics from each implementation.
Evaluating Age Verification Solutions: What to Look For
Selecting the right age verification solution requires systematic evaluation. After helping dozens of clients through this process, I've developed a comprehensive framework that consistently identifies the best fit for specific business needs.
The evaluation must begin with regulatory compliance requirements. Every age verification system I recommend must demonstrably satisfy applicable regulations—whether that's the Online Safety Act 2023 for UK-based platforms, COPPA for services targeting American children, or industry-specific requirements like those governing online gambling. I always request compliance documentation and audit reports from vendors before recommending their solutions.
Software as a service (SaaS) delivery models offer significant advantages for most businesses. Cloud-based age verification eliminates infrastructure management overhead while providing automatic updates and scaling capabilities. However, I also evaluate whether vendors maintain ISO/IEC 27001 certification, which demonstrates commitment to information security management best practices.
Balancing Security, Compliance, and User Experience
This balance represents the eternal challenge in age verification. I've worked with clients who initially implemented such rigorous verification that conversion rates dropped 40%. The solution isn't compromising security—it's optimizing the process.
Best practices I recommend for minimizing user friction while maintaining verification integrity:
- Implement progressive verification (start simple, escalate only when necessary)
- Use device fingerprinting to reduce repeat verification requirements
- Offer multiple verification methods so users can choose their preferred approach
- Optimize for mobile experiences where most verification failures occur
- Provide clear, encouraging instructions rather than intimidating legal language
- Test extensively with real users before full deployment
Fraud prevention and user experience aren't opposing forces—they're complementary when implemented thoughtfully. In my experience, the most successful implementations achieve sub-30-second verification times while maintaining false positive rates below 2%. Regulatory compliance requirements establish the floor; user experience optimization determines ceiling for adoption success.
Integration Capabilities and Technical Requirements
Technical integration capabilities make or break age verification implementations. I always evaluate API documentation quality, endpoint performance, error handling robustness, webhook support for asynchronous verification, and rate limiting policies during vendor assessment.
Software development kits (SDKs) dramatically accelerate implementation. When working with clients, I prefer vendors offering native SDKs for iOS, Android, JavaScript, and major backend languages. Quality SDKs include sample code, comprehensive documentation, and responsive technical support—luxuries that save weeks during implementation.
I always ask vendors about their authentication protocols. OAuth 2.0 support is non-negotiable for modern implementations, and I prefer platforms offering granular permission controls and API key rotation capabilities. These features aren't just technical niceties; they're essential security requirements that protect both the business and its customers.
Choosing an Age Verification Tool
When I work with clients, I always walk them through a systematic selection process:
| Step | Action | Key Questions |
| 1 | Define your use case | What content/products require age verification? What are your compliance obligations? |
| 2 | Review verification methods | Which verification methods satisfy your regulatory requirements? What accuracy levels do you need? |
| 3 | Assess technology integration | Does the solution offer APIs/SDKs for your platform? What's the expected implementation timeline? |
| 4 | Prioritize compliance | Does the vendor provide compliance documentation? Have they passed third-party audits? |
| 5 | Analyze data privacy | How is personal data collected, stored, and deleted? Is encryption implemented throughout? |
| 6 | Test for scalability | Can the system handle your peak verification volumes? What are the rate limits and costs at scale? |
| 7 | Evaluate false positive management | What's the false positive rate? How are edge cases handled? |
| 8 | Review cost structure | What's the per-verification cost? Are there volume discounts or minimum commitments? |
This framework has consistently helped my clients select appropriate verification tools that satisfy their regulatory compliance requirements while respecting user personal data protected under the General Data Protection Regulation and similar frameworks. The vendors that meet these criteria while offering robust encryption for data protection typically deliver the best long-term value.
Top Age Verification Software Providers Compared
Through extensive experience implementing solutions from various vendors, I've developed nuanced perspectives on the leading age verification providers. Let me share my analysis of the platforms I most frequently recommend to clients.
The age verification market includes dozens of identity verification service providers, but several consistently deliver exceptional results across diverse age verification system implementations. Each provider brings unique strengths, and the right choice depends entirely on your specific business requirements, compliance needs, and user demographic.
| Provider | Best For | Key Strengths | Compliance Coverage | Integration Ease | Approximate Cost |
| iDenfy | SMBs, E-commerce | User-friendly, quick setup, competitive pricing | GDPR, KYC, AML | Excellent | $0.60-$1.50/check |
| Jumio | Enterprise, High-risk | Advanced biometrics, global coverage, accuracy | Comprehensive global | Excellent | $2.00-$4.00/check |
| Trulioo | Global operations | 195+ country coverage, identity verification | Global compliance | Very good | $1.50-$3.00/check |
| Onfido | Tech companies | AI-driven, real-time verification, developer-friendly | EU/US focus | Excellent | $1.00-$2.50/check |
| Yoti | Privacy-focused | Reusable digital ID, privacy-by-design | GDPR-focused | Good | $0.50-$1.20/check |
Enterprise-Level Solutions for High-Compliance Industries
For clients in heavily regulated industries—particularly online gambling, adult entertainment, financial services, and pharmaceuticals—I typically recommend enterprise-grade solutions that prioritize accuracy and audit trails over cost optimization.

Jumio consistently excels in these high-stakes environments. I've implemented Jumio for several online gambling clients who face strict regulatory scrutiny. Their biometric liveness detection is among the most sophisticated I've encountered, effectively preventing spoofing attempts using photos or videos. The platform offers real-time verification with detailed audit trails that satisfy even the most demanding regulators. When I worked with a major gambling operator expanding into the UK market under the Online Safety Act 2023, Jumio's comprehensive compliance documentation proved invaluable during the licensing process.

Trulioo brings unmatched global reach—essential for businesses operating internationally. Their identity verification service covers 195 countries with localized compliance expertise. I've found Trulioo particularly valuable for clients who need to verify ages in emerging markets where document standards vary significantly. Their ability to cross-reference multiple data sources compensates for regions with less sophisticated identity infrastructure.
Both platforms offer dedicated account management and compliance consulting—services worth the premium pricing when regulatory compliance stakes are high. The average cost per verification ranges $2-4, but the investment protects against regulatory fines that can reach millions.
Mid-Market and SMB-Friendly Options
Not every business needs enterprise-level capabilities or pricing. For e-commerce platforms, content creators, and smaller operators, I frequently recommend more accessible solutions that deliver solid verification without enterprise complexity.

iDenfy has become my go-to recommendation for small and medium-sized businesses. I've implemented iDenfy for numerous e-commerce clients selling age-restricted products—from premium wines to tobacco accessories. The platform offers straightforward software as a service delivery with simple pricing and quick implementation. Most of my clients complete iDenfy integration in under two weeks, even with limited technical resources.
The platform's user experience particularly impresses me. iDenfy's mobile-optimized verification flow achieves completion rates 20-30% higher than some enterprise platforms I've tested—crucial for consumer-facing businesses where friction directly impacts revenue. For businesses processing under 10,000 verifications monthly, iDenfy typically offers the best value proposition I've encountered.
Age Verification Methods Comparison
Different providers emphasize different verification methodologies. Understanding these distinctions helps match providers to specific use cases.
Identity document verification forms the foundation for most providers, but implementation quality varies dramatically. Jumio's document verification leverages advanced machine learning that I've seen correctly identify fraudulent documents that fooled other systems. Their optical character recognition accuracy exceeds 99% even with damaged or poor-quality documents—something I particularly appreciate when working with clients who serve older demographics less comfortable with technology.
Facial recognition systems integrated with age estimation represent the frontier of frictionless verification. I've implemented these for social media clients who need reasonable age assurance without creating conversion friction. The technology analyzes facial features to estimate age within 2-3 year ranges—sufficient for many use cases. However, I always caution clients that facial recognition alone typically doesn't satisfy strict regulatory requirements for high-risk industries.
Biometric liveness detection prevents spoofing—a critical feature I insist upon for any serious implementation. Basic systems accept photographs, but sophisticated biometric systems require users to perform actions (blink, smile, turn head) that prove they're physically present during verification. This functionality has prevented countless fraud attempts across my client implementations.
The best providers, including Jumio and iDenfy, combine multiple verification methods. They might start with facial recognition for initial screening, escalate to identity document verification when confidence is insufficient, and employ biometric liveness detection throughout to prevent fraud. This layered approach balances user experience with security—the sweet spot I constantly pursue when architecting verification systems.
Implementation Guide: Successfully Deploying Age Verification
Successfully implementing an age verification system requires more than selecting a vendor and integrating their API. I've learned through dozens of implementations that systematic planning and execution separate successful deployments from problematic ones.
The implementation timeline typically spans 4-12 weeks depending on system complexity and organizational readiness. I guide clients through a structured process that minimizes disruption while ensuring thorough testing before production deployment.
My standard implementation framework:
- Requirements documentation (Week 1) – Document all verification scenarios, compliance requirements, integration points, and success metrics
- Vendor API integration (Weeks 2-3) – Integrate vendor API or software development kit, implement error handling, configure webhooks for asynchronous processing
- User experience design (Week 3-4) – Design verification flows, create instructional content, optimize for mobile experiences
- Security implementation (Week 4) – Configure encryption for data transmission and storage, implement authentication controls, establish data retention policies
- Compliance validation (Week 5-6) – Verify regulatory compliance documentation, conduct privacy impact assessment, prepare audit documentation
- Testing phase (Weeks 6-8) – Execute comprehensive testing protocol, gather user feedback, optimize for edge cases
- Soft launch (Week 9) – Deploy to limited user subset, monitor performance metrics, refine based on real-world data
- Full production (Week 10) – Complete rollout with ongoing monitoring
- Optimization (Ongoing) – Continuous improvement through automation and analytics-driven refinement
Throughout implementation, I emphasize the importance of comprehensive testing across diverse scenarios—different document types, various lighting conditions, edge cases like minors attempting to use adult documents. Automation opportunities emerge during this phase, particularly around exception handling and fraud detection.
Testing and Optimization Strategies
Testing represents the make-or-break phase of age verification implementation. I've salvaged multiple client projects that initially appeared doomed by applying systematic testing and optimization methodologies.
My testing protocol includes:
- Functional testing – Verify all verification methods work correctly across supported document types, devices, browsers, and network conditions. I test using real identity documents (with permission) to understand actual user experiences.
- False positive analysis – Deliberately attempt to trigger false rejections using valid documents. In my experience, false positive rates above 3% significantly damage user experience and conversion. Using analytics, I identify patterns in false rejections and work with vendors to refine their algorithms.
- Fraud testing – Attempt verification using fraudulent documents, photos of documents, screenshots, and other common fraud techniques. This adversarial testing helps identify vulnerabilities before bad actors exploit them.
- User experience optimization – Monitor completion rates, abandonment points, and time-to-complete metrics. I've consistently improved conversion 15-25% through systematic user experience refinement based on real user behavioral data.
- Load testing – Verify the system handles peak verification volumes without degradation. I once discovered a client's implementation would fail during peak holiday traffic—catching this during testing prevented a catastrophic production failure.
The optimization phase never truly ends. I establish continuous monitoring using analytics platforms that track verification success rates, processing times, fraud attempt patterns, and user feedback. This data informs ongoing refinement that incrementally improves both security and usability.
Future Trends in Age Verification Technology
The age verification system landscape continues evolving rapidly. Based on patterns I'm observing across my client work and industry developments, several trends will fundamentally reshape how businesses verify ages in coming years.
Advanced biometric technologies are becoming increasingly sophisticated and accurate. I'm particularly excited about neural network models that can estimate age from facial features with accuracy approaching human-level performance. These systems will enable genuinely frictionless verification—users simply look at their device camera for 2-3 seconds and receive instant age confirmation. I'm already testing early implementations of this technology with select clients.
Facial recognition systems are incorporating deepfake detection capabilities—a critical evolution as synthetic media becomes more sophisticated. The verification systems I'm implementing now include liveness detection specifically designed to identify AI-generated faces and deepfake videos. This cat-and-mouse game between fraud techniques and detection capabilities will intensify.
Automation powered by artificial intelligence will dramatically reduce manual review requirements. Current systems still flag 10-15% of verification attempts for human review; next-generation platforms I'm tracking promise to reduce this to 2-3% while maintaining accuracy. This transformation will substantially reduce operational costs while improving processing speeds.
Reusable digital identity credentials represent the most transformative trend I'm watching. Rather than verifying age separately for each service, users will eventually maintain verified digital identities that can be selectively shared across platforms. This approach dramatically improves user experience while potentially offering stronger privacy protections—users prove they meet age requirements without sharing unnecessary personal data.
Industry-Specific Age Verification Requirements
Different industries face distinct verification challenges and regulatory requirements. Throughout my career serving clients across diverse sectors, I've developed specialized expertise in industry-specific compliance requirements.
Online Gambling and Gaming

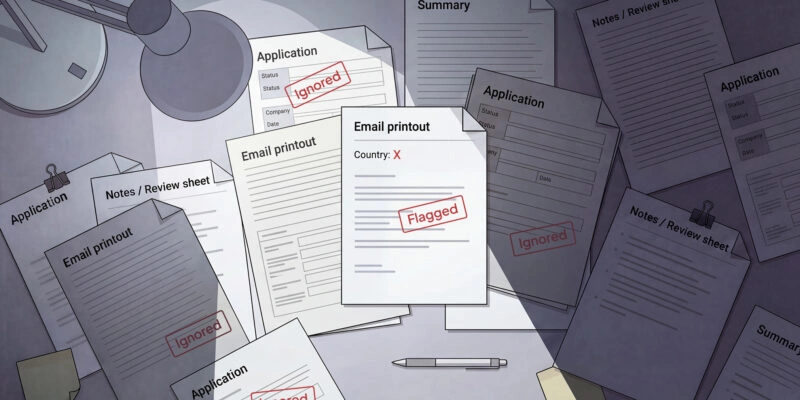
Online gambling faces the strictest age verification requirements I encounter. Gambling regulations universally mandate robust age verification before allowing any betting activity. The Online Safety Act 2023 in the UK now requires gambling operators to implement enhanced verification that prevents minors from accessing gambling services.
When I work with gambling clients, I emphasize:
- Document-based verification as minimum standard (no self-declaration)
- Verification before any gameplay or deposit (zero tolerance for delayed verification)
- Ongoing monitoring for account sharing or credential theft
- Comprehensive audit trails for regulatory inspections
- Integration with responsible gambling tools that flag concerning patterns
I've implemented verification systems for online casinos, sports betting platforms, and skill-gaming sites. The stakes are uniquely high—a single minor accessing gambling services can trigger license revocation and massive fines.
E-commerce and Retail

E-commerce platforms selling age-restricted products—alcohol, tobacco, vaping products, supplements—face increasingly rigorous verification requirements. Several U.S. states now mandate age verification for online tobacco and alcohol sales that rivals in-person ID checking requirements.
For e-commerce clients, I recommend:
- Verification at checkout for age-restricted products
- Address verification to confirm delivery recipient can accept restricted products
- Driver verification integration for delivery confirmation
- Clear documentation of verification for potential audits
- Refund policies that account for failed age verification
The Children's Online Privacy Protection Act (COPPA) adds complexity for platforms that might attract children. Any service collecting personal data from users under 13 must implement parental consent mechanisms—effectively requiring age verification for adult users to distinguish parents from children.
Social Media and Content Platforms

The Online Safety Act 2023 fundamentally transformed age verification requirements for social media and user-generated content platforms operating in the UK. Platforms that could expose children to harmful content must implement age verification or age assurance measures.
I've consulted with several social media clients navigating these new requirements. The challenge is implementing verification that doesn't create excessive friction for billions of users. Most platforms I work with use risk-based approaches—simple age estimation for general access, escalating to document verification for features carrying higher risk.
Financial Services
Financial services integrate age verification into broader know your customer (KYC) and anti-money laundering (AML) requirements. Banks, payment processors, and fintech applications must verify customer identities including age verification during account creation.
The verification requirements for financial services typically exceed those in other industries. I implement multi-factor verification incorporating document verification, biometric authentication, database cross-referencing against credit bureaus, and sometimes even in-person verification for high-value accounts.
Why Your Business Needs Reliable Online Age Verification
Beyond regulatory compliance, reliable age verification systems deliver substantial business value that justifies investment even when not legally mandated.
Key business benefits I consistently observe:
- Fraud reduction – Robust verification prevents identity theft, account takeover, and fraudulent purchases. One retail client reduced chargebacks 31% within six months of implementing comprehensive age verification.
- Enhanced regulatory compliance – Proactive verification prevents costly regulatory penalties while demonstrating good faith compliance efforts that favorably influence regulators during audits.
- Strengthened computer security – Age verification adds authentication layers that complement existing security measures, making systems more resistant to cybercrime attempts.
- Improved customer trust – Customers increasingly expect businesses to protect children online. Implementing verification signals corporate responsibility and builds brand trust.
- Competitive differentiation – In industries where verification isn't yet mandatory, early adoption creates competitive advantages with safety-conscious consumers.
- Reduced liability exposure – Documented verification efforts provide legal defenses against claims that businesses facilitated minor access to restricted content or products.
The businesses that gain maximum value from age verification treat it as strategic infrastructure rather than compliance checkbox. When I work with forward-thinking clients, we architect verification systems that support business growth rather than merely preventing regulatory problems. The investment pays dividends through reduced fraud, enhanced security, and stronger customer relationships.
Age Verification Privacy and Data Protection Considerations
Age verification inherently requires collecting and processing personal data—creating privacy obligations that responsible businesses must address thoughtfully.
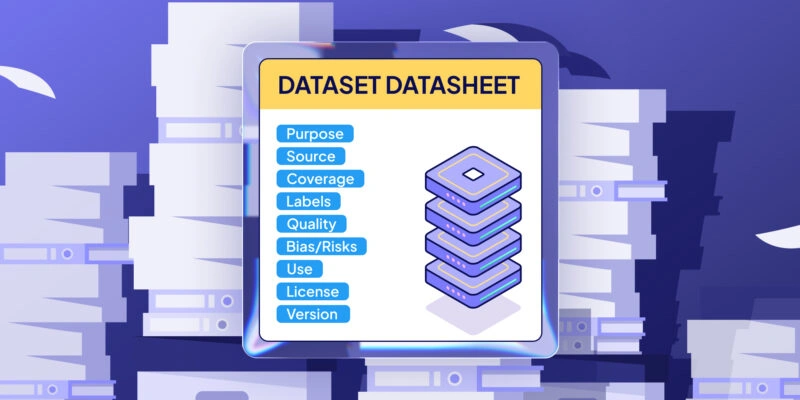
The General Data Protection Regulation (GDPR) establishes comprehensive requirements for handling personal data during verification. Having guided numerous clients through GDPR compliance, I emphasize several critical principles:
Data minimization – Collect only information absolutely necessary for age verification. If estimating age from facial features suffices, don't collect identity documents containing addresses and ID numbers. I've helped clients reduce data collection 60-70% while maintaining verification efficacy.
Purpose limitation – Use verification data exclusively for age verification purposes. Reusing this data for marketing, profiling, or other purposes without separate consent violates GDPR principles and undermines user trust.
Storage limitation – Retain verification data only as long as legally required or reasonably necessary. I typically recommend 30-90 day retention periods unless specific regulations mandate longer retention. Automated deletion policies reduce privacy risks and storage costs.
Security safeguards – Implement encryption for all personal data both in transit and at rest. Use AES-256 encryption as minimum standard. Restrict access through granular permission controls. Monitor for unauthorized access attempts.
Transparency – Clearly explain to users what data you collect, why you need it, how long you retain it, and who you share it with. Provide easily accessible privacy policies specific to age verification rather than burying these details in general privacy policies.
Information privacy principles demand that age verification systems respect user dignity while satisfying business and regulatory needs. The best implementations achieve this balance through technical and organizational measures that protect data throughout its lifecycle.
I encourage clients to pursue privacy-enhancing approaches like:
- Age estimation technologies that determine sufficient age without collecting identity documents
- Zero-knowledge verification protocols where verification occurs without the platform accessing underlying personal data
- Federated identity systems where users maintain control over their verified credentials
- Regular privacy impact assessments that identify and mitigate emerging risks
The businesses that excel at privacy-protective verification gain customer trust and regulatory goodwill while avoiding the costly data breaches that plague companies treating personal data carelessly.
Conclusion: Selecting the Right Age Verification Solution for Your Business
Selecting the right age verification system represents a critical decision with lasting implications for regulatory compliance, user experience, and business operations.
Throughout this guide, I've shared insights from years implementing verification systems across diverse industries. The key considerations I emphasize with every client remain consistent:
Start with compliance requirements – Understand precisely which regulations apply to your business and what verification standards they mandate. Build compliance documentation from day one.
Prioritize user experience – Select verification methods appropriate for your user demographics and risk profile. Excessive friction destroys conversion while inadequate verification creates compliance exposure.
Evaluate privacy implications – Implement data minimization, encryption, and retention policies that respect user privacy while satisfying verification needs.
Plan for scale – Choose solutions that can handle growth without requiring complete rebuilding. Consider per-verification costs at projected volumes.
Invest in implementation quality – Rushed implementations create technical debt and compliance gaps. Allocate sufficient time for testing and optimization.
Treat verification as strategic infrastructure – Age verification done right strengthens security, reduces fraud, and builds customer trust beyond mere compliance checkbox.
The businesses that excel at age verification approach it as opportunity rather than burden. They implement verification systems that satisfy current regulatory requirements while positioning for emerging regulations. They balance security with usability. They respect user privacy while preventing fraud.
I hope this guide empowers you to select and implement age verification solutions that serve your business needs, satisfy regulatory obligations, and respect your customers. The landscape continues evolving, but the fundamental principles of thoughtful, user-centered verification endure.
Final checklist for age verification success:
- Documented compliance requirements for all applicable regulations
- Evaluated vendors based on compliance capabilities, user experience, technical fit, privacy protections, and cost structure
- Selected verification methods appropriate for your risk profile and user demographics
- Designed implementation plan with adequate testing and optimization phases
- Established privacy policies and data protection measures
- Prepared compliance documentation for regulatory audits
- Created monitoring systems for ongoing performance optimization
- Allocated resources for continuous improvement as technology and regulations evolve
Age verification represents a journey rather than destination. The businesses that succeed continuously refine their approaches based on user feedback, regulatory developments, and technological advances. Whether you're implementing your first verification system or optimizing existing infrastructure, the principles I've shared provide a roadmap for sustainable success.
📑 Article Disclaimer
The information contained in this article is provided for general informational and editorial purposes only. The content reflects the opinions, research, and editorial judgment of the author(s) at the time of publication and does not constitute professional, legal, financial, or business advice of any kind.
No Endorsement or Warranty
The mention, ranking, or listing of any company, product, or service within this article does not constitute an endorsement, recommendation, or guarantee of quality, reliability, or fitness for any particular purpose. The publisher makes no representations or warranties, express or implied, regarding the accuracy, completeness, timeliness, or suitability of the information provided.
Independence of Judgment
Readers are strongly encouraged to conduct their own independent research and due diligence before engaging with, contracting, or entering into any business relationship with any of the companies referenced herein. The inclusion or exclusion of any company does not imply a definitive assessment of its capabilities, compliance, or business conduct.
No Liability
To the fullest extent permitted by applicable law, the publisher, editors, authors, and any affiliated parties expressly disclaim all liability for any direct, indirect, incidental, consequential, or punitive damages arising from reliance on the information contained in this article, including but not limited to decisions made on the basis of company rankings or descriptions.
Third-Party Information
Certain information presented in this article may be sourced from third parties, publicly available data, or company self-disclosures. The publisher does not independently verify all such information and assumes no responsibility for errors, omissions, or changes occurring after the date of publication.
No Legal or Regulatory Advice
Nothing in this article should be construed as legal, regulatory, or compliance guidance. Data collection practices are subject to varying laws and regulations across jurisdictions. Readers should consult qualified legal counsel regarding their specific circumstances and applicable law.
Subject to Change
The data collection industry is dynamic. Company rankings, capabilities, and reputations are subject to change. This article represents a snapshot in time and may not reflect current market conditions.
By accessing and reading this article, you acknowledge and agree to the terms of this disclaimer.
Frequently Asked Questions (FAQ)
Online age verification employs multiple methods I regularly implement: document verification (analyzing government-issued IDs), biometric age estimation (using facial recognition systems), database cross-referencing, and credential verification. The process typically captures user data, encrypts transmission, authenticates information against databases or through document analysis, and returns verification results within seconds while maintaining privacy through data minimization.
Throughout my career, I’ve implemented age verification for online gambling (legally required), e-commerce platforms selling alcohol or tobacco, social media and content platforms, financial services, adult entertainment, and gaming platforms. Industries facing regulatory scrutiny or serving minors benefit enormously. Even businesses without legal mandates gain competitive advantages through enhanced security and customer trust.
I regularly deploy five primary methods: identity document verification (highest accuracy, 95-99%), facial recognition with age estimation (85-95% accuracy, lowest friction), biometric analysis including liveness detection, database verification against credit bureaus or public records, and credit card verification. Each method suits different use cases—I help clients select approaches balancing their compliance requirements with user experience needs.
In my implementations, robust age verification reduces fraud by 30-50% through multi-factor authentication, document authenticity verification, biometric liveness detection preventing spoofing, identity theft prevention, and detection of account sharing or credential misuse. It enhances computer security by adding authentication layers that deter cybercrime. One e-commerce client reduced chargebacks 31% after implementing comprehensive verification.
The best age verification tools I recommend feature high accuracy (>95%), regulatory compliance documentation for GDPR and applicable laws, quick processing (under 30 seconds), minimal user friction, robust API integration, comprehensive data encryption, excellent documentation and support, reasonable pricing structures, and scalability. I prioritize vendors like iDenfy for SMBs and Jumio for enterprises based on these criteria.
Age verification costs vary significantly by provider and volume. I typically see $0.50-$1.50 per verification for SMB-friendly platforms like iDenfy, $1.00-$2.50 for mid-market solutions, and $2.00-$4.00 for enterprise platforms like Jumio with advanced biometrics. Volume discounts apply at scale. Consider total costs including integration, ongoing maintenance, and false positive handling when budgeting implementation.
Legal requirements depend on your industry and jurisdiction. Online gambling requires verification universally. The Online Safety Act 2023 mandates verification for UK platforms exposing children to harmful content. COPPA requires parental consent verification for services collecting data from users under 13. E-commerce businesses selling age-restricted products face increasing state-level requirements. I recommend consulting legal counsel to assess your specific obligations.
Based on extensive testing, document verification offers highest accuracy (95-99%) but medium friction, facial recognition provides good accuracy (85-95%) with minimal friction, biometric analysis delivers 90-97% accuracy with low friction, and database verification achieves 80-90% accuracy instantly. I select methods based on risk tolerance—gambling requires document verification while social media often uses facial recognition for acceptable accuracy with minimal abandonment.
Yes, modern age verification solutions integrate seamlessly with e-commerce platforms through APIs and SDKs. I’ve successfully integrated verification with Shopify, WooCommerce, Magento, BigCommerce, and custom platforms. Most implementations take 2-4 weeks. Vendors like iDenfy and Jumio offer pre-built plugins for popular platforms. The identity verification service connects at checkout for age-restricted products, verifying before completing purchases.